Network Services with Hybrid Cloud for a Service
Posted by Brian Bradley on Apr 6, 2021 10:00:00 AM
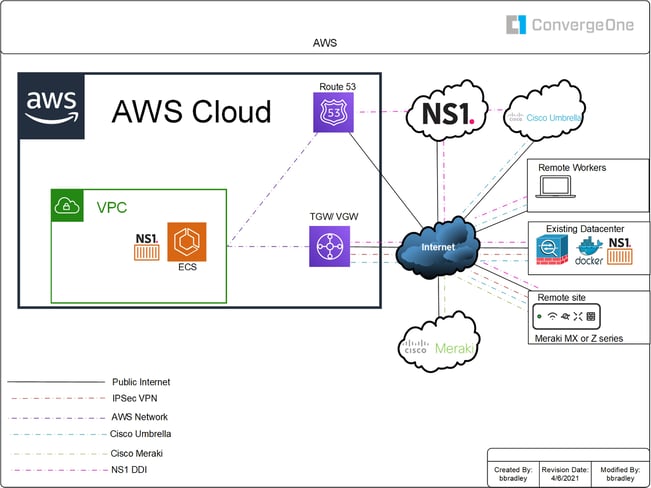
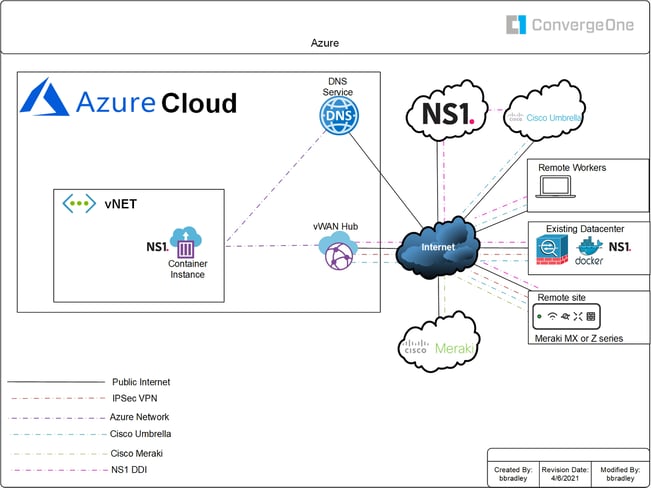
The Cisco Meraki MX and Z3 have the native ability via presets to do Meraki AutoVPN or AWS/Azure-native IPSec VPN. Both your existing facilities and Public Cloud presence can also host and accept IPSec. AWS Cloud Hub or Azure vHub can host and accept and function as—you guessed it—an IPSec Hub.
It's actually an AWS Virtual Gateway or Transit Gateway (VGW/TGW) using VPN attachments or Azure Virtual Wan Hub (vHUB) facing the Public Internet. The VGW/TGW/vHUB can also form a single/double IPSec overlay link back to your existing facilities and services. Secure both sides of the tunnel(s) by permitting only those public IP addresses from the Cloud and existing data center. This allows your existing facilities firewalls and services to focus on inspecting traffic from one source: the Cloud. Remote users that have software VPN can connect to a Public/Private Cloud-hosted firewall in the same VPC/vNET as your site’s VPN.
A Meraki vMX could also be hosted within the VPC/vNET if a SD-WAN architecture is desired. The software VPN firewall would allow the vMX to interconnect with SDWAN sites and allow remote-access VPN.
What other network services can we offload to the Cloud once connected?
NS1 as a Global Traffic Manager (GTM) can handle your Public DNS steering toward the public-facing Multi-Cloud edge. You can set public Internet-bound DNS inspection to Cisco Umbrella on remote client devices as we scale the edge of the network and securely welcome the outside into any Public/Private Cloud-hosted applications.
Now, the network transport via VPN/SD-WAN can be secured to our applications hosted with the Hybrid Cloud. Selecting the optimal internal server target used to be the job of the Local Traffic Manager (LTM) load balancer. NS1 can replace it and steer your traffic between your Public/Private Cloud-hosted applications based on a plethora of logic-driven metrics, using dynamic application steering during maintenance and other Hybrid/Multi-Cloud scheduled/unscheduled events in an automated manner with alerting fashion for maximum applications availability.
DHCP-DNS-IP address management (DDI) can be hosted at your Public/Private Cloud via NS1 docker containers. This allows the steering of your Meraki sites, remote VPN traffic, and any other securely connected sites application traffic while also providing private IP address space management across ALL sites and Public/Private Cloud platforms.
These four service portals combined (Meraki/Umbrella/NS1/AWS-Azure) form a powerful and flexible, remotely-managed, and secure connection using best-in-class API-driven technologies for dynamic application steering and URL traffic inspection for your securely inspected connected users. Since it’s API-driven and service-oriented, you can even develop your own portal with the desired feeds and controls based on what is important to your company.
API-integrated services can also provide Identity authentication for users in the above architecture for both infrastructure and application access. I will leave that as the "take some time to think about it” topic as a next step.
ConvergeOne can help you learn, integrate, and apply any of the network services for supporting the business outcomes required by your organization. Reliable transport, secure access, and application steering services matter for every organization. The time is now to dynamically route, steer, and authenticate your organization with new API-driven tools.
LEARN MORE ABOUT CISCO MERAKI
The simplicity and efficiency of Meraki introduces enormous benefits in terms of operations, allowing network staff to scale significantly more than with a traditional infrastructure. Contact your ConvergeOne National Account Manager or reach out to us below to have a discussion about what your business could look like with Meraki in it.
Topics: Cisco, Enterprise Networking


